Description The utility 'openssl' is used to generate the key and CSR. This utility comes with the OpenSSL package and is usually installed under /usr/local/ssl/bin. Type the following command at the prompt: openssl ecparam -out privatekey.key -name prime256v1. As of version 2.6.2 DidiSoft OpenPGP Library for Java fully supports Elliptic Curve cryptography (ECC) in OpenPGP as defined in RFC 6637. In this chapter we are going to make a short introduction to the new ECC encryption and illustrate how to generate your first ECC OpenPGP key pair.
-->
To sign an assembly with a strong name, you must have a public/private key pair. This public and private cryptographic key pair is used during compilation to create a strong-named assembly. You can create a key pair using the Strong Name tool (Sn.exe). Key pair files usually have an .snk extension.
Note
In Visual Studio, the C# and Visual Basic project property pages include a Signing tab that enables you to select existing key files or to generate new key files without using Sn.exe. In Visual C++, you can specify the location of an existing key file in the Advanced property page in the Linker section of the Configuration Properties section of the Property Pages window. The use of the AssemblyKeyFileAttribute attribute to identify key file pairs was made obsolete beginning with Visual Studio 2005.
Create a key pair
To create a key pair, at a command prompt, type the following command:
Are you trying to find a supply of a free of charge multi player cd-key generator but devoid of results? Nevertheless on this web you can obtain primarily operating key generators. Revolutionary.io beta key generator.
sn –k <file name>
In this command, file name is the name of the output file containing the key pair.
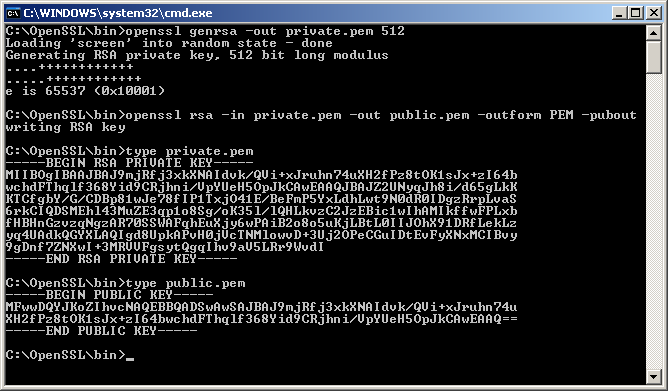
The following example creates a key pair called sgKey.snk.
Openssl Generate Keypair
If you intend to delay sign an assembly and you control the whole key pair (which is unlikely outside test scenarios), you can use the following commands to generate a key pair and then extract the public key from it into a separate file. First, create the key pair:
Next, extract the public key from the key pair and copy it to a separate file:
Once you create the key pair, you must put the file where the strong name signing tools can find it.
When signing an assembly with a strong name, the Assembly Linker (Al.exe) looks for the key file relative to the current directory and to the output directory. When using command-line compilers, you can simply copy the key to the current directory containing your code modules.
Openssl Generate Key Pair Ssh
If you are using an earlier version of Visual Studio that does not have a Signing tab in the project properties, the recommended key file location is the project directory with the file attribute specified as follows:
See also
| *** RSA |
| # Generate self-signed certificate with RSA 4096 key-pair |
| openssl req -x509 -nodes -days 3650 -newkey rsa:4096 -keyout rsakey.pem -out rsacert.pem |
| # print private and public key |
| openssl rsa -in rsakey.pem -text -noout |
| # print certificate |
| openssl x509 -in rsacert.pem -text -noout |
| # generate PKCS#12 container |
| openssl pkcs12 -export -inkey rsakey.pem -in rsacert.pem -out rsacred.p12 |
| *** ECDSA |
| # Generate self-signed certificate with ECDSA using two common curves |
| openssl req -x509 -nodes -days 3650 -newkey ec:<(openssl ecparam -name prime256v1) -keyout ecdsakey.pem -out ecdsacert.pem |
| openssl req -x509 -nodes -days 3650 -newkey ec:<(openssl ecparam -name secp384r1) -keyout ecdsakey.pem -out ecdsacert.pem |
| # print private and public key + curve name |
| openssl ec -in ecdsakey.pem -text -noout |
| # print certificate |
| openssl x509 -in ecdsacert.pem -text -noout |
| # generate container |
| openssl pkcs12 -export -inkey ecdsakey.pem -in ecdsacert.pem -out ecdsacred.p12 |
| Which curve to choose? |
| http://security.stackexchange.com/questions/78621/which-elliptic-curve-should-i-use |
| 'Interoperability' means that you would probably prefer it if SSL clients can actually |
| connect to your server; otherwise, having a SSL server would be rather pointless. |
| This simplifies the question a lot: in practice, average clients only support two curves, |
| the ones which are designated in so-called NSA Suite B: these are NIST curves P-256 and |
| P-384 (in OpenSSL, they are designated as, respectively, 'prime256v1' and 'secp384r1'). |
| If you use any other curve, then some widespread Web browsers (e.g. Internet Explorer, |
| Firefox..) will be unable to talk to your server. |
| *** DSA |
| # generate both key and DSA parameters (both will be stored in dsakey.pem) |
| openssl dsaparam -genkey 1024 -out dsakey.pem |
| openssl req -x509 -new -days 3650 -key dsakey.pem -out dsacert.pem |
| # print private and public key with DSA params |
| openssl dsa -in dsakey.pem -text -noout |
| # print certificate |
| openssl x509 -in dsacert.pem -text -noout |
| # print only DSA params from key file |
| openssl dsaparam -in dsakey.pem -text -noout |
| # generate container |
| openssl pkcs12 -export -inkey dsakey.pem -in dsacert.pem -out dsacred.p12 |
| *** Test TLS connection |
| openssl s_server -accept 1443 -www -key key.pem -cert cert.pem |
| openssl s_client -showcerts -connect localhost:1443 -CAfile cert.pem |
Openssl Generate Ecc Key Pair Key
commented Jan 29, 2018
|
This is very useful |